There are a lot of security concerns with PowerShell DSC. Perhaps the first that jumps to our mind is, “our configurations contain a lot of important and proprietary information!” True. Also true is, “if someone can modify our configurations, then they can control our environment.” So we will try and address both of these concerns.
Securing Configurations
All uploaded configurations are automatically signed with our code signing certificate. So you do not have to take care of securing your configurations.
During client registration, an additional certificate is installed on the client to identify requests from trusted nodes.
Securing the Pull Server
Our DSC implementation does not run on a web server. We are running containers behind an API gateway with user authentication.
Configure for Strong Cryptography
How to configure .NET Framework to support strong cryptography. Set the SchUseStrongCrypto registry setting to DWORD:00000001. This value disables the RC4 stream cipher and requires a restart. For more information about this setting, see Microsoft Security Advisory 296038.
Make sure to set the following registry keys on any computer that communicates across the network with a TLS 1.2-enabled system. For example, configuration manager clients, remote site system roles not installed on the site server, and the site server itself.
For 32-bit applications that are running on 32-bit OSs and for 64-bit applications that are running on 64-bit OSs, update the following sub-key values:
Registry
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NETFramework\v2.0.50727]
"SystemDefaultTlsVersions" = dword:00000001
"SchUseStrongCrypto" = dword:00000001
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NETFramework\v4.0.30319]
"SystemDefaultTlsVersions" = dword:00000001
"SchUseStrongCrypto" = dword:00000001
For 32-bit applications that are running on 64-bit OSs, update the following subkey values:
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\.NETFramework\v2.0.50727]
"SystemDefaultTlsVersions" = dword:00000001
"SchUseStrongCrypto" = dword:00000001
[HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\.NETFramework\v4.0.30319]
"SystemDefaultTlsVersions" = dword:00000001
"SchUseStrongCrypto" = dword:00000001
The SchUseStrongCrypto setting allows .NET to use TLS 1.1 and TLS 1.2. The SystemDefaultTlsVersions setting allows .NET to use the OS configuration. For more information, see TLS best practices with .NET Framework.
Proxy Configuration for Nodes
In order for PowerShell DSC nodes being forced to use a proxy server to communicate with the cloud hosted backend, some adjustments to the node configuration must be done before registering the node.
DSC does not communicate in a user context and therefore uses the SYSTEM context.
For DSC to connect successfully and register the node, adjust the following lines inside the machine.config in your .NET installation directory. You should find the file in these locations:
32-bit
**%windir%\Microsoft.NET\Framework\[version]\config\machine.config**
64-bit
**%windir%\Microsoft.NET\Framework64\[version]\config\machine.config**
[version] should be equal to v1.0.3705, v1.1.4322, v2.0.50727 or v4.0.30319. v3.0 and v3.5 just contain additional assemblies to v2.0.50727 so there should be no config\machine.config. v4.5.x and v4.6.x are stored inside v4.0.30319.
Then add the following lines:
<defaultProxy>
<proxy autoDetect="false" bypassonlocal="false" proxyaddress="http://127.0.0.1:8888" />
</defaultProxy>
</system.net>
PowerShell DSC configuration encryption
PowerShell DSC configurations that are uploaded while adding the configuration are going to be encrypted by using a certificate that is provided by XOAP.
This happens in two cases:
- Adding a configuration by manually uploading configuration files (as ps1) with the upload wizard
- Adding a configuration by using the DSC Configuration Wizard
After the file is encrypted it is converted to base64 string and pushed to a dedicated backend storage location.
If you are uploading a compiled mof file, it will not be encrypted.
Configuration decryption
In case of losing the original configuration file or another emergency case, you are able to decrypt your uploaded .mof configurations.
What you need for this is:
- Your encrypted configuration (downloaded from XOAP)
- Certificate for decryption
- Password for decryption
- Decrypt script (Decrypt.ps1)
Download files for decryption
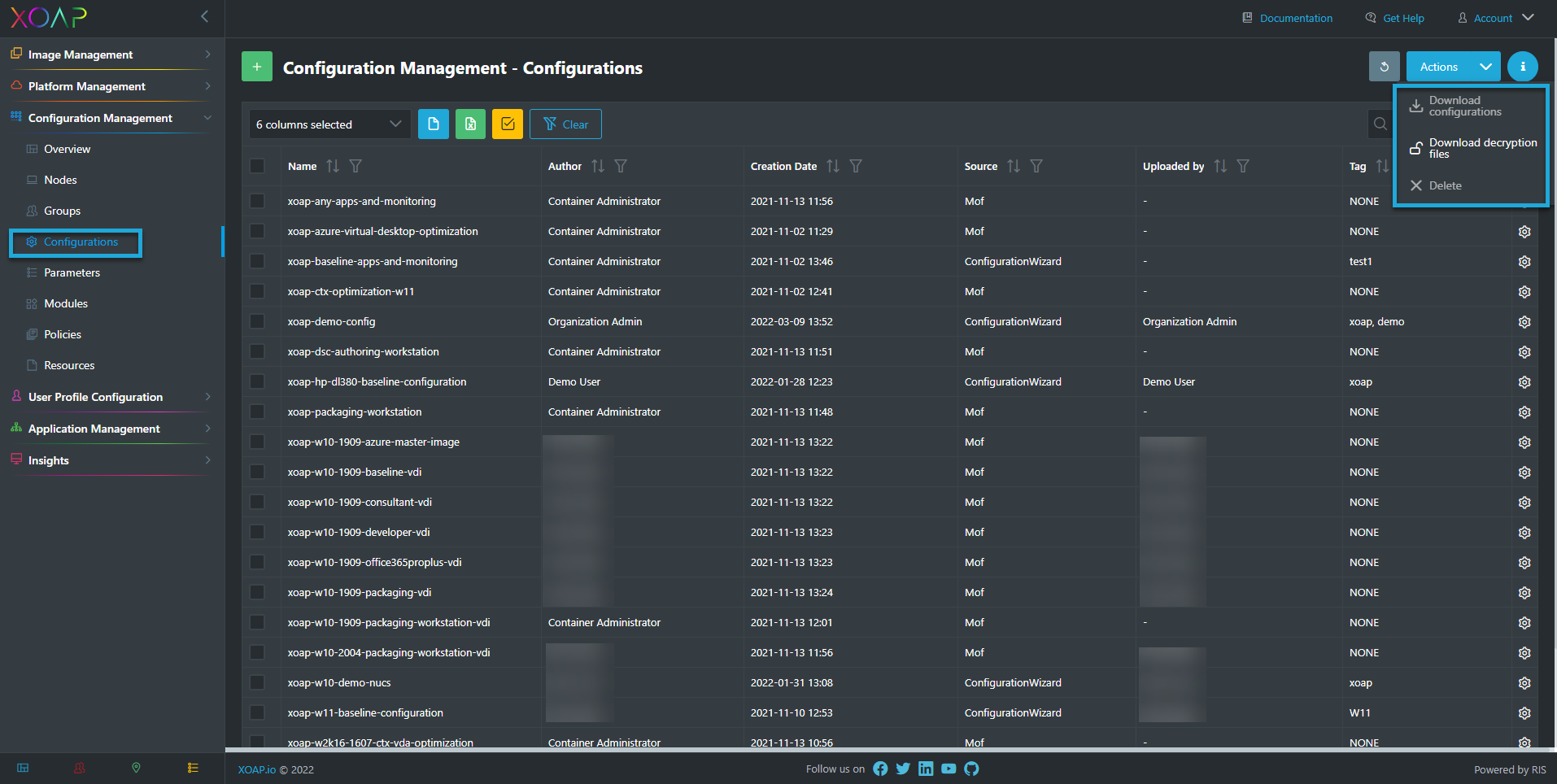
All of the above can be downloaded from the config.XO configurations area in XOAP:
Download decryption files contains all the files mentioned above. Now you just need to download your encrypted configuration.
Example
In this example, we put all the files needed into the path: C:\temp\Decrypt Configuration:
- Open PowerShell and call the Decrypt.ps1 script
- Enter the parameters: CertificateFilePath, EncryptedFilePath, OutputFilePath
.\Decrypt.ps1 -CertificatePath "C:\temp\Decrypt Configuration\cert.pfx" -EncryptedFilePath "C:\temp\Decrypt Configuration\Baseline20H2W10.mof" -OutputFilePath "C:\temp\Decrypt Configuration\Decrypted.mof"